Our Programs
BTSADV programs provide safe spaces for survivors to share their stories and have access to the resources they need.
Donate
Doing the work takes time and money. Find out how you can help BTSADV by donating today!
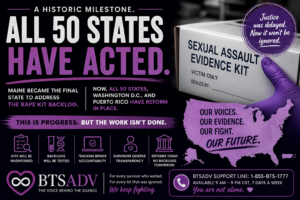
Join Us In The Fight Against Domestic Violence
You can start your journey with BTSADV today.
Simply sign up to volunteer, or donate right now!



Making A Difference An Impact Change Survivors Hopeful

Find Your Voice,
Share Your Journey
Sharing your story can not only make a difference, but it can also set you free. And possibly help someone else.
Break your silence today!
Creating A Better Life for Survivors of Domestic Violence
Every dollar counts towards helping survivors of domestic violence and abuse find the support and resources they need.
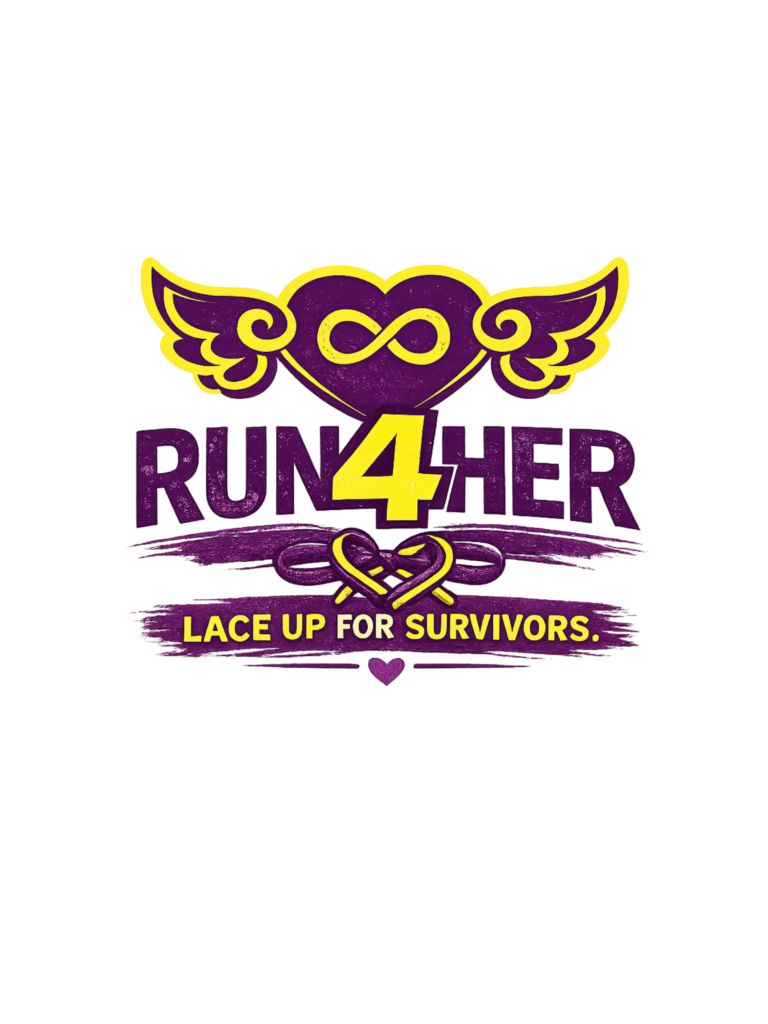
Join a powerful 31 day journey of healing, hope, and movement. Whether you’re walking a mile a day or supporting a survivor, every step you take brings awareness, strength, and support to those affected by domestic violence. Let’s run, reflect, and rise—together.
Funds raised through the Run4Her Challenge help support our survivor scholarship program, with a portion of every registration and donation directly funding educational opportunities for those rebuilding after domestic violence.
https://www.run4herchallenge.com/ https://www.run4herchallenge.com/shop
HALO Memorials
BTSADV keeps memorial for those we have lost to DV alongside families and friends.
Read the stories of these beautiful humans to see why we keep doing what we do.



Survivor Stories
and Blogs
Survivor
Toolkits
We have put together an all encompassing toolkit for survivors.
From how to collect evidence for court, to finding out more about how to handle your finances, BTSADV has the resources you need.



Shop Our Store
Support the organization by shopping our merchandise!
Every penny goes towards helping survivors.